In a stark reminder of the relentless evolution of cyber threats, a sophisticated Vietnamese-linked operation, codenamed “AccountDumpling” by Guardio, has reportedly compromised an estimated 30,000 Facebook accounts. This extensive phishing campaign ingeniously exploited Google AppSheet as a “phishing relay” to bypass conventional spam filters and ensnare unsuspecting users, ultimately funneling stolen credentials into a thriving illicit marketplace.
Security researcher Shaked Chen, in a report shared with The Hacker News, underscored the advanced nature of this threat: “What we found wasn’t a single phishing kit. It was a living operation with real-time operator panels, advanced evasion, continuous evolution and a criminal-commercial loop that quietly feeds on the same accounts it helps steal back.” This revelation paints a grim picture of a highly organized and adaptive cybercriminal enterprise.
The Deceptive Mechanism: Google AppSheet as a Phishing Relay
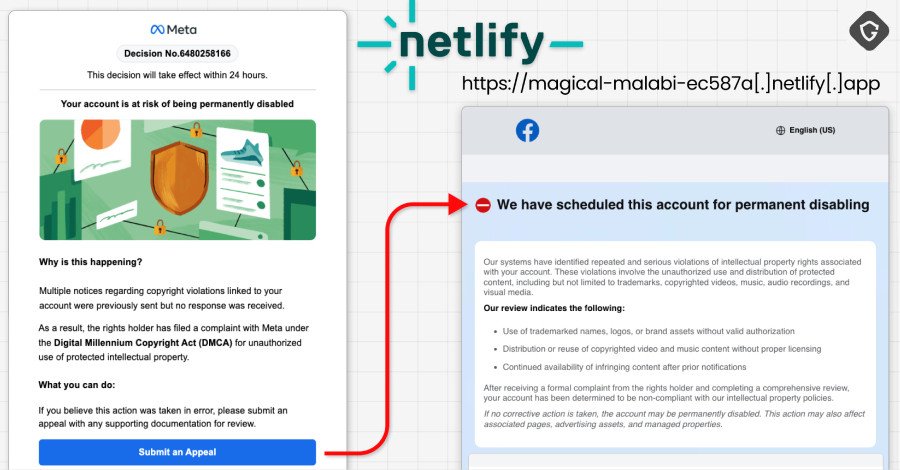
The genesis of the AccountDumpling attacks lies in meticulously crafted phishing emails. These messages, masquerading as urgent communications from “Meta Support,” targeted Facebook Business account owners. The emails falsely warned recipients that their accounts faced permanent deletion unless an immediate appeal was submitted.
Crucially, these deceptive emails were dispatched from a legitimate Google AppSheet address (noreply@appsheet.com
). This clever tactic allowed the phishing attempts to sail past many spam filters, lending an air of authenticity that significantly increased their success rate. Users, gripped by a false sense of urgency, were then directed to fabricated web pages designed to meticulously harvest their login credentials.
An Evolving Arsenal of Lures
The AccountDumpling campaign is not static; it continuously adapts its lures to induce what Guardio terms “Meta-related panic.” Over recent weeks, the threat actors have diversified their pretexts, ranging from:
- Account disablement warnings
- Fictitious copyright infringement complaints
- Mandatory verification reviews
- Executive
recruitment opportunities
- Urgent Facebook login alerts
This dynamic approach ensures a broad attack surface and keeps potential victims perpetually on edge, making it harder for users to discern legitimate communications from malicious ones.
The Four Pillars of Deception
Guardio’s investigation uncovered four primary clusters of attack vectors employed by the AccountDumpling operation, each demonstrating a distinct level of technical sophistication:
Netlify-Hosted Help Centers
This cluster involved phishing pages hosted on Netlify, meticulously designed to mimic legitimate Facebook help centers. Beyond just account takeover, these pages were engineered to collect sensitive personal data, including dates of birth, phone numbers, and even government-issued ID photos. All harvested data was then systematically forwarded to attacker-controlled Telegram channels.
Blue Badge & Privacy Center Scams
Another tactic leveraged lures related to “blue badge” verification or “Meta | Privacy Center” pages. Victims were guided to Vercel-hosted sites featuring a bogus CAPTCHA check, a common trick to deter automated analysis. After this hurdle, users were directed to phishing landing pages to collect contact details, business information, credentials (often after a forced retry for perceived errors), and even critical two-factor authentication (2FA) codes, all exfiltrated to Telegram channels.
Malicious Google Drive PDFs
In a more document-centric approach, the threat actors distributed Google Drive-hosted PDFs. These documents masqueraded as official instructions for completing account verification. Upon interaction, they directed users to pages designed to collect passwords, 2FA codes, government ID photos, and even browser screenshots via html2canvas. Intriguingly, these malicious PDFs were generated using a free Canva account, leaving a crucial breadcrumb for attribution.
Elaborate Fake Job Offers
The fourth cluster involved highly personalized fake job offers. Impersonating renowned companies such as WhatsApp, Meta, Adobe, Pinterest, Apple, and Coca-Cola, these lures aimed to build rapport with recipients. Victims were then prompted to join a call or continue discussions on attacker-controlled websites, likely leading to further credential harvesting or malware deployment.
Global Reach and Attribution
The cumulative impact of these campaigns is staggering, with approximately 30,000 victim records identified across the first three clusters alone. The victims are geographically diverse, primarily located in the U.S., Italy, Canada, the Philippines, India, Spain, Australia, the U.K., Brazil, and Mexico, many of whom have been locked out of their own accounts.
The “smoking gun” for attribution emerged from the metadata of the Canva-generated PDFs. This metadata explicitly listed a Vietnamese name, “PHẠM TÀI TÂN,” as the author. Further open-source intelligence revealed a website (phamtaitan[.]vn) offering digital marketing services, which, in a February 2023 X post, claimed to specialize in “providing digital marketing services, marketing resources, and consulting on effective digital marketing strategies.”
Chen concluded, “Taken together, they form a consistent picture of a large, Vietnamese-based, mega operation. This campaign is bigger than a single AppSheet abuse. It’s a window into the dark market around stolen Facebook assets, where access, business identity, ad reputation, and even account recovery have all become tradable commodities. Another entry in the pattern we keep surfacing: trusted platforms repurposed as delivery, hosting, and monetization layers.”
The AccountDumpling operation serves as a critical reminder of the sophisticated and evolving nature of cybercrime. Users and businesses alike must remain vigilant, scrutinizing unsolicited communications and verifying the authenticity of requests, especially those demanding sensitive information.
For more details, visit our website.
Source: Link







Leave a comment