The Evolving Threat of Software Supply Chain Attacks
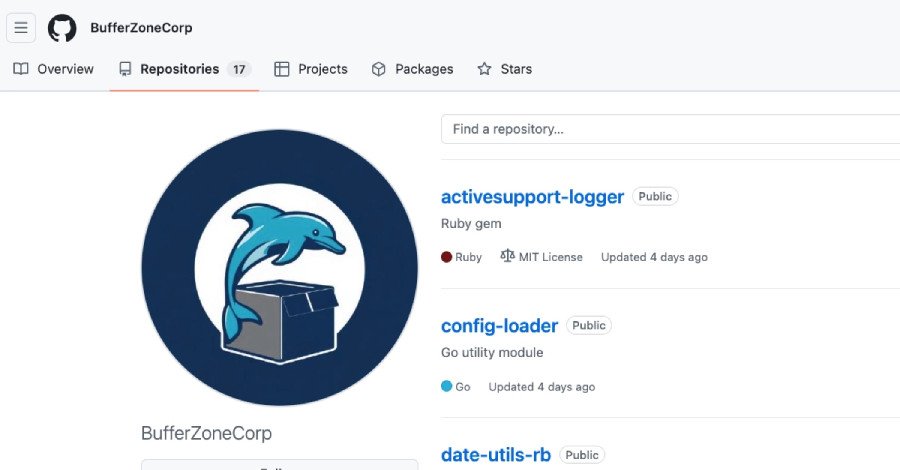
A sophisticated new software supply chain attack campaign has emerged, leveraging seemingly innocuous “sleeper packages” to infiltrate continuous integration (CI) pipelines and steal sensitive credentials. This alarming activity, attributed to the GitHub account “BufferZoneCorp,” highlights a critical vulnerability in the development ecosystem, targeting both RubyGems and Go modules.
The digital landscape is constantly under siege, and software supply chain attacks represent one of the most insidious threats. In this latest campaign, attackers employed a two-pronged strategy: first, deploying benign-looking “sleeper” packages, and then, after a period of dormancy, pushing malicious updates designed for credential theft, GitHub Actions tampering, and establishing SSH persistence.
Deceptive Disguises and Attribution
The malicious packages were cleverly named to mimic popular and trusted modules, such as activesupport-logger and go-retryablehttp
, making them difficult to distinguish from legitimate libraries. This tactic aimed to trick unsuspecting developers into downloading and integrating them into their projects. The orchestrator behind this campaign, “BufferZoneCorp,” has since had their associated RubyGems yanked and Go modules blocked, but the incident serves as a stark reminder of the constant vigilance required in software development.
The identified malicious libraries include:
- Ruby Gems: knot-activesupport-logger, knot-devise-jwt-helper, knot-rack-session-store, knot-rails-assets-pipeline, knot-rspec-formatter-json, knot-date-utils-rb (Sleeper), knot-simple-formatter (Sleeper)
- Go Modules: github[.]com/BufferZoneCorp/go-metrics-sdk, github[.]com/BufferZoneCorp/go-weather-sdk, github[.]com/BufferZoneCorp/go-retryablehttp, github[.]com/BufferZoneCorp/go-stdlib-ext, github[.]com/BufferZoneCorp/grpc-client, github[.]com/BufferZoneCorp/net-helper, github[.]com/BufferZoneCorp/config-loader, github[.]com/BufferZoneCorp/log-core (Sleeper), github[.]com/BufferZoneCorp/go-envconfig (Sleeper)
A Dual-Ecosystem Compromise: Ruby and Go Targets
Socket security researcher Kirill Boychenko emphasized the breadth of this campaign, stating, “The account is part of a software supply chain campaign targeting developers, CI runners, and build environments across two ecosystems.” The attack vector cleverly adapts its payload depending on the targeted environment.
Ruby Gems: A Direct Path to Credential Theft
For Ruby environments, the malicious gems were engineered for immediate credential harvesting upon installation. They meticulously scoured systems for critical environment variables, SSH keys, AWS secrets, .npmrc, .netrc, GitHub CLI configurations, and RubyGems credentials. This stolen treasure trove of data was then exfiltrated to an attacker-controlled Webhook[.]site endpoint, providing attackers with direct access to sensitive developer resources.
Go Modules: Advanced Tampering and Persistence
The Go modules exhibited a more sophisticated array of capabilities. Beyond data theft, they were designed to actively tamper with GitHub Actions workflows, inject fake Go wrappers, and establish persistent access by adding a hard-coded SSH public key to “~/.ssh/authorized_keys” on compromised hosts. Boychenko detailed the cunning execution: “The module executes through init(), detects GITHUB_ENV and GITHUB_PATH, sets HTTP_PROXY and HTTPS_PROXY, writes a fake go executable into a cache directory, and appends that directory to the workflow path so the wrapper is selected before the real binary. That wrapper can then intercept or influence later go executions while still passing control to the legitimate binary to avoid breaking the job.” This intricate method allowed the attackers to maintain control without immediately disrupting the legitimate build process, making detection even harder.
Protecting Your Development Environment
Given the stealth and sophistication of these attacks, immediate action is crucial for any developer or organization that may have installed these packages.
Recommended Mitigation Steps
Users are strongly advised to:
- Remove Malicious Packages: Immediately uninstall any of the listed Ruby gems or Go modules from all systems.
- Security Audit: Conduct a thorough review for any signs of unauthorized access to sensitive files or unexpected modifications to “~/.ssh/authorized_keys.”
- Credential Rotation: Rotate all exposed credentials, including API keys, tokens, and passwords, that may have been present in the compromised environments.
- Network Monitoring: Scrutinize network logs for any outbound HTTPS traffic directed towards the identified exfiltration point (Webhook[.]site) or other suspicious destinations.
This campaign serves as a powerful reminder that software supply chain security is paramount. Developers and organizations must adopt robust security practices, including rigorous vetting of third-party dependencies, implementing least privilege principles, and continuous monitoring of build environments, to safeguard against such evolving threats. Stay informed and secure your pipelines.
For more details, visit our website.
Source: Link








Leave a comment