In a concerning development for software supply chain security, cybersecurity giant Checkmarx has confirmed yet another breach, this time involving a modified version of its Jenkins AST plugin. The incident, attributed to the notorious cybercrime group TeamPCP, comes mere weeks after a significant attack on Checkmarx’s KICS Docker image and other developer tools.
TeamPCP Strikes Again: Jenkins Plugin Compromised
Checkmarx issued an urgent advisory over the weekend, confirming that a malicious iteration of its Jenkins AST plugin found its way onto the Jenkins Marketplace. The company strongly urged users to verify their plugin versions, specifically recommending the use of version 2.0.13-829.vc72453fa_1c16 published on or before December 17, 2025. While Checkmarx has since released a new, secure version (2.0.13-848.v76e89de8a_053) on both GitHub and the Jenkins Marketplace, the specifics of how the compromised version was initially published remain undisclosed.
A Pattern of Attacks: From KICS to Jenkins
This latest breach marks a troubling continuation of TeamPCP’s targeted campaign against Checkmarx. Just a few weeks prior, the same group was implicated in the compromise of Checkmarx’s KICS Docker image, two VS Code extensions, and a GitHub Actions workflow. These earlier attacks were designed to inject credential-stealing malware, which subsequently led to the brief compromise of the Bitwarden CLI npm package, allowing the harvesting of sensitive developer secrets.
TeamPCP has been an active threat since March 2026, orchestrating a widespread campaign that leverages the inherent trust within the software supply chain to disseminate its malware and broaden its illicit reach.
The Defacement and Lingering Questions
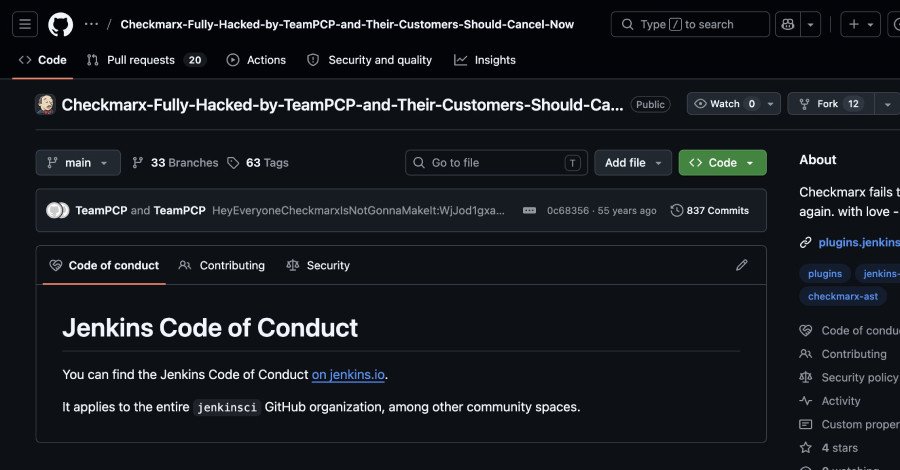
Further details, brought to light by security researcher Adnan Khan and SOCRadar, paint a stark picture of the attack’s audacity. TeamPCP reportedly gained unauthorized access to the plugin’s GitHub repository, subsequently renaming it to a provocative "Checkmarx-Fully-Hacked-by-TeamPCP-and-Their-Customers-Should-Cancel-Now." The defaced repository also bore a taunting description: "Checkmarx fails to rotate secrets again. with love – TeamPCP."
Incomplete Remediation or Persistent Foothold?
The swift recurrence of attacks raises critical questions about Checkmarx’s security posture following the initial March incident. SOCRadar’s analysis suggests two primary possibilities:
- Incomplete Remediation: The initial response might have failed to fully rotate all compromised credentials.
- Persistent Foothold: TeamPCP may have maintained an undetected presence within Checkmarx’s systems after the first breach.
“A second Checkmarx incident happening this soon suggests the group is actively watching for re-entry points, testing the depth of past remediations, and capitalizing on any gaps,” SOCRadar emphasized. This ongoing cat-and-mouse game underscores the sophisticated and persistent nature of modern cyber threats targeting critical software infrastructure.
For more details, visit our website.
Source: Link







Leave a comment