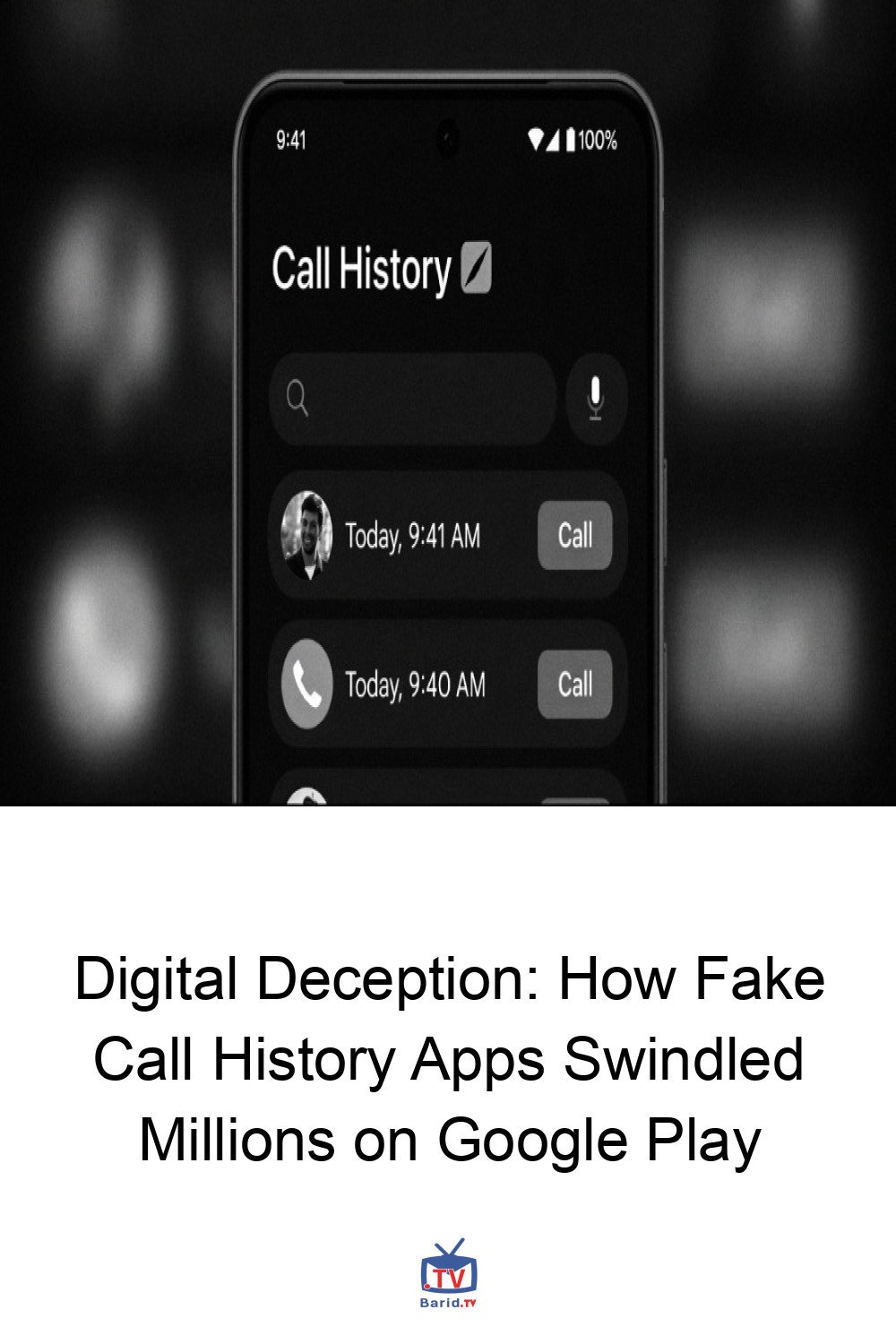
In a stark reminder of the persistent threats lurking within official app stores, cybersecurity experts have unearthed a sophisticated scam that duped millions of Android users. A network of 28 fraudulent applications, masquerading as tools to access call histories for any phone number, collectively amassed over 7.3 million downloads on the Google Play Store before their eventual removal. This elaborate scheme, codenamed “CallPhantom” by Slovakian cybersecurity firm ESET, primarily targeted users in India and the broader Asia-Pacific region, luring them into costly subscriptions that delivered nothing but fabricated data.
The Illusion of Information: How CallPhantom Operated
At the heart of the CallPhantom operation was a simple yet effective deception. The apps promised an irresistible feature: instant access to call histories, SMS records, and even WhatsApp call logs for any phone number. ESET security researcher Lukáš Štefanko revealed, “To unlock this supposed feature, users are asked to pay — but all they get in return is randomly generated data.” This meant victims were paying for a service that never truly existed, receiving entirely fake phone numbers and names directly embedded within the app’s source code.
Building False Trust and Global Reach
The perpetrators went to cunning lengths to establish a veneer of legitimacy. At least one of the offending apps was published under the developer name “Indian gov.in,” a deliberate attempt to mimic an official government entity and instill a false sense of trust among unsuspecting users. While the scam had a global footprint, its primary focus on India and the Asia-Pacific region highlights a targeted approach, exploiting regional user bases and payment systems.
The Financial Trap: Multi-pronged Payment Schemes
The monetization strategy employed by the CallPhantom apps was multifaceted, ensuring a wide net for potential victims. Payments were solicited through several channels:
Official Google Play Billing:
Leveraging the legitimate subscription system, which ironically meant Google received a cut of the fraudulent transactions.- Third-Party UPI Apps: Exploiting India’s widely adopted Unified Payments Interface (UPI) system, with integrations for popular platforms like Google Pay, Walmart-backed PhonePe, and Paytm. This method, along with direct card forms, explicitly violated Google’s developer policies.
- Direct Payment Card Forms: Some apps featured in-app checkout forms for credit/debit card details, bypassing official channels entirely.
Deceptive Tactics to Secure Payment
Beyond the initial lure, the apps employed an additional layer of trickery to pressure users into payment. If a user attempted to exit an app without subscribing, a deceptive notification would appear, falsely claiming that a call history for a specified number had already been successfully sent to their email. Clicking this notification, however, would merely redirect the user back to the subscription screen, reinforcing the scam. Subscription plans varied widely, ranging from approximately $6 to a hefty $80, extracting significant sums from victims.
The Aftermath and Lessons Learned
Following ESET’s discovery and report, the 28 fraudulent apps were promptly removed from the Google Play Store. Users who had fallen victim to these scams should have had their subscriptions automatically canceled. What makes this particular campaign noteworthy is the simplicity of the apps: they featured basic user interfaces and, crucially, did not request any sensitive device permissions. This lack of intrusive permissions made them appear less suspicious, allowing them to evade detection for longer and accumulate millions of downloads.
This incident serves as a critical reminder for all smartphone users to exercise extreme caution when downloading new applications. Always scrutinize developer names, read reviews, and be wary of apps promising extraordinary features, especially those requiring payment for data that seems too good to be true. The digital landscape demands constant vigilance to protect against such sophisticated financial scams.
For more details, visit our website.
Source: Link








Leave a comment