The Unsung Heroes: Why Tier 1 Analysts Are Your SOC’s Most Critical Asset
In the high-stakes world of cybersecurity, the Security Operations Center (SOC) stands as the digital fortress protecting an organization‘s most valuable assets. Yet, within this critical defense, CISOs often grapple with an uncomfortable truth: the very individuals on the front lines, tasked with real-time threat detection, are typically those with the least experience. These Tier 1 analysts, while pivotal, are also the most susceptible to the cognitive and organizational pressures that silently erode SOC performance over time.
The Paradox at the Gate: Burdened by Volume, Undermined by Vulnerability
Tier 1 is the crucible where the vast majority of alerts are processed, initial triage is performed, and critical escalation decisions are made. It’s the foundation upon which the entire SOC’s responsiveness rests. However, this crucial layer is often built on structurally fragile ground. A relentless deluge of alerts, coupled with high turnover rates and the inherent inexperience of entry-level analysts, creates an environment where even the most sophisticated detection rules can fail to translate into timely, accurate responses.
This creates a profound paradox:
- Tier 1 performance directly dictates overall SOC effectiveness.
Yet, Tier 1 is frequently the least supported, least empowered, and most cognitively overloaded segment of the security team.
The Silent Erosion: The Toll on Tier 1 Analysts
The daily avalanche of alerts takes a significant toll on Tier 1 analysts, manifesting in several critical issues:
- Alert Fatigue: Constant exposure to high volumes dulls sensitivity to genuine threats.
- Decision Fatigue: The sheer number of micro-decisions degrades judgment quality over time.
- Cognitive Overload: Too many dashboards and insufficient context lead to mental exhaustion.
- False-Positive Conditioning: When 90% of alerts are benign, a default skepticism can lead to missed threats.
- Burnout and Turnover: The cumulative effect leads to exhaustion, staff churn, and the loss of invaluable institutional memory.
For CISOs, these aren’t merely HR challenges; they represent significant business risks. When Tier 1 hesitates, misses, or delays an escalation, the consequences are severe:
- Dwell time increases, allowing threats to persist undetected.
- Incident response costs skyrocket.
- Overall detection quality plummets.
- Executive
confidence in the security posture erodes.
A weak Tier 1 transforms the entire SOC from a proactive, predictive force into a reactive, firefighting unit.
The Core Engine Room: Monitoring and Triage as Business-Critical Workflows
At its heart, Tier 1 is responsible for two foundational SOC processes: monitoring and alert triage. These are often perceived as routine, almost mundane tasks, but their efficiency directly impacts an organization’s bottom line and resilience.
- Monitoring: This involves the continuous ingestion of signals from across the entire digital environment—endpoints, networks, cloud infrastructure, identity systems—and applying detection logic to surface events of potential concern.
- Triage: Following monitoring, triage is the structured, human-driven process of evaluating these events, assigning severity, diligently ruling out false positives, and determining whether escalation to higher tiers is warranted.
While seemingly straightforward—watching telemetry, sorting alerts—these workflows are, in essence, revenue protection mechanisms. They directly influence Mean Time To Respond (MTTR), Mean Time To Detect (MTTD), and the overall efficiency of resource allocation. When these workflows falter:
- Tier 2 and Tier 3 analysts become overwhelmed by noise.
- Incident response efforts are delayed, increasing damage.
- Business disruption expands exponentially.
- Operational costs surge.
- Regulatory exposure and compliance risks grow.
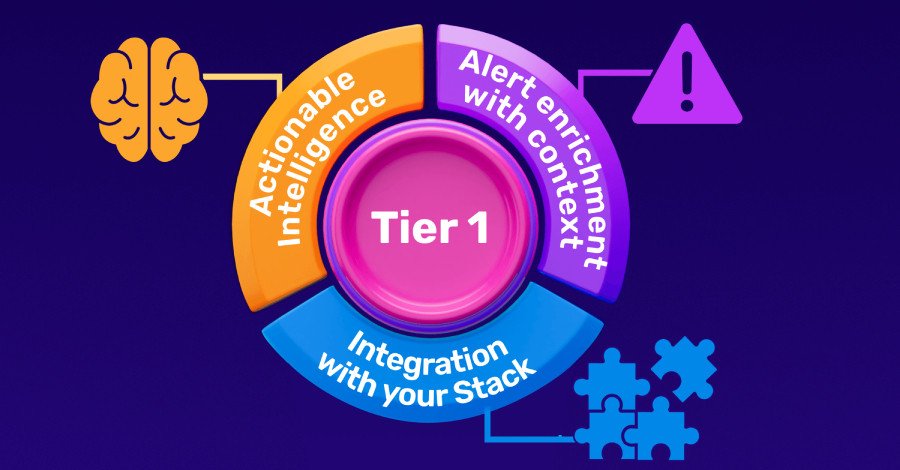
Intelligence as Oxygen: Fueling Tier 1 Effectiveness
A Tier 1 analyst cannot operate effectively in a vacuum. Raw alerts, devoid of context, are merely digital shadows. Actionable threat intelligence is the oxygen that transforms this data into decisive action. When a Tier 1 analyst asks, “Is this connected to an active campaign targeting our sector?”, robust threat intelligence provides immediate, critical answers:
- IOC (Indicator of Compromise) validation.
- Campaign context and adversary profiles.
- TTP (Tactics, Techniques, and Procedures) mapping.
- Infrastructure associations and attacker footprints.
- Malware family attribution.
Tier 1 analysts, making the most time-sensitive decisions with the least inherent contextual background, need threat intelligence more urgently than any other role in the SOC. Integrating actionable feeds and lookup enrichment directly into SOC workflows is paramount for accelerating detection and bolstering operational resilience. This directly reduces dwell time and significantly increases confidence in security decisions.
Step 1: Detect What Others Miss – Powering Monitoring with Live Threat Intelligence Feeds
The first, and arguably most impactful, step towards building a high-impact Tier 1 is to fundamentally upgrade the intelligence foundation of your monitoring capabilities. Traditional SOC environments often rely on detection rules built from static signatures or behavioral heuristics. While effective initially, these methods degrade over time as adversaries constantly adapt and evolve their tactics.
Actionable threat intelligence feeds continuously inject fresh, verified indicators of compromise (IOCs) directly into your detection infrastructure. This paradigm shift means that instead of merely flagging anomalies and requiring an analyst to research them, a feed-enriched monitoring layer flags activity that has already been confirmed as malicious through real-world analysis. Detections are no longer based on statistical deviation but on behavioral ground truth.
The operational impact on early detection is profound. It dramatically compresses the window of exposure, allowing for quicker containment and significantly reducing the overall cost of an eventual incident. For instance, platforms like ANY.RUN provide Threat Intelligence Feeds that aggregate indicators (malicious IPs, URLs, domains) directly from a continuously operating malware analysis sandbox. This means the data reflects active threat activity observed through dynamic execution analysis, offering a real-time, behavioral perspective rather than relying solely on historical reporting or third-party aggregations. Adversaries who modify their malware to evade static signatures find it far more difficult to evade such dynamic behavioral observation.
These TI Feeds, typically delivered in industry-standard STIX and MISP formats, integrate seamlessly with existing SIEMs and other security tools, enabling a more proactive and informed defense.
For more details, visit our website.
Source: Link