The Deceptive Call: A New Wave of Havoc C2 Attacks
In a chilling new campaign, threat actors are masquerading as benevolent IT support, deploying the sophisticated Havoc command-and-control (C2) framework as a prelude to devastating data exfiltration or ransomware attacks. Identified by cybersecurity firm Huntress across five partner organizations, these intrusions highlight a disturbing evolution in social engineering and malware delivery, demonstrating a rapid, aggressive progression from initial access to widespread network compromise.
The modus operandi bears a striking resemblance to past attacks orchestrated by affiliates of the notorious Black Basta ransomware operation. While Black Basta itself has been quiet since internal chat logs were leaked last year, the persistence of its playbook suggests two unsettling possibilities: either former affiliates have migrated to new operations, or rival groups have adopted their highly effective social engineering tactics.
Anatomy of a Sophisticated Scam: From Spam to System Takeover
The attack chain is meticulously designed, beginning with a deluge of spam emails aimed at overwhelming a target’s inbox. This initial chaos sets the stage for the crucial next step: a phone call from a supposed IT desk. Posing as helpful support staff, the threat actors convince recipients to grant remote access to their machines, typically via legitimate tools like Quick Assist or AnyDesk, under the guise of resolving the fabricated spam issue.
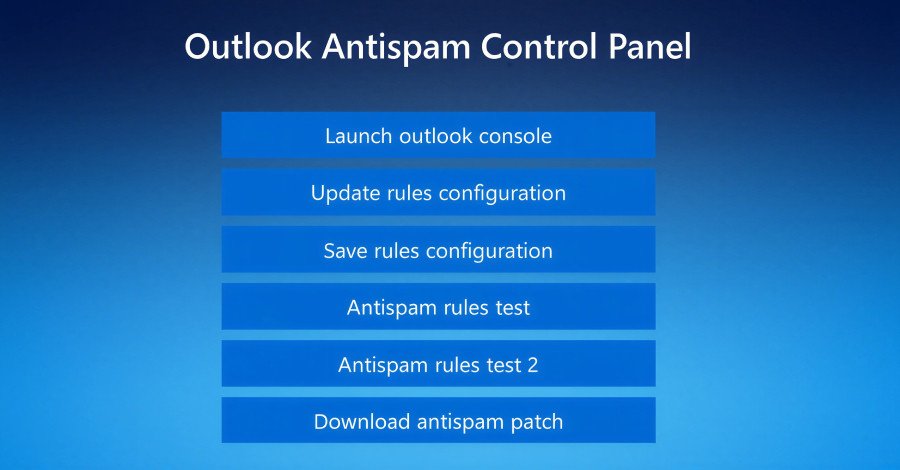
Once remote access is established, the adversaries move with alarming speed. They direct the victim’s browser to a fake landing page, cleverly hosted on Amazon Web Services (AWS) and impersonating Microsoft. Here, victims are instructed to enter their email address to access an Outlook anti-spam rules update system. Clicking a button to “Update rules configuration” triggers a script that displays an overlay, prompting for the user’s password. This dual-purpose mechanism not only harvests credentials but also lends an air of authenticity to the interaction, making the user believe the process is genuine.
Advanced Evasion: Havoc C2 and EDR Bypass
The core of the attack lies in the download of a supposed anti-spam patch. This “patch” executes a legitimate binary (such as “ADNotificationManager.exe”, “DLPUserAgent.exe”, or “Werfault.exe”) to sideload a malicious Dynamic Link Library (DLL). This DLL payload is engineered for defense evasion, spawning a thread that contains the Havoc shellcode payload, effectively deploying the Demon agent.
One identified DLL, “vcruntime140_1.dll,” incorporates advanced techniques to sidestep detection by security software. These include control flow obfuscation, timing-based delay loops, and sophisticated methods like Hell’s Gate and Halo’s Gate. These techniques enable the malware to hook `ntdll.dll` functions, effectively bypassing Endpoint Detection and Response (EDR) solutions and allowing the Havoc Demon to establish a foothold undetected.
Rapid Lateral Movement and Persistent Control
With the Havoc Demon successfully deployed on the initial host, the threat actors initiate rapid lateral movement across the victim’s network. While the initial social engineering and malware delivery showcase intricate techniques, the subsequent hands-on-keyboard activity is surprisingly direct. This includes creating scheduled tasks to relaunch the Havoc Demon payload upon every system reboot, ensuring persistent remote access.
Interestingly, the attackers also diversify their persistence mechanisms by deploying legitimate remote monitoring and management (RMM) tools like Level RMM and XEOX on some compromised hosts, alongside or instead of Havoc. This strategic use of both custom malware and legitimate tools underscores their adaptability and determination to maintain control.
Key Takeaways for Organizational Defense
This campaign offers critical insights into the evolving threat landscape:
- Social Engineering Sophistication:
Threat actors are increasingly willing to impersonate IT staff and even call personal phone numbers to enhance their success rates.
- Advanced Evasion for All: Defense evasion techniques, once reserved for state-sponsored operations or attacks on large enterprises, are now becoming commonplace in commodity malware.
- Customized Commodity Malware: Attackers are customizing readily available malware to bypass pattern-based signatures, making detection more challenging.
- Speed and Persistence: The aggressive speed from initial compromise to lateral movement, coupled with diverse persistence methods, demands swift incident response capabilities.
What begins as a seemingly innocuous phone call from “IT support” can rapidly escalate into a fully instrumented network compromise. This campaign serves as a stark case study in how modern adversaries layer sophistication and persistence, leveraging human vulnerabilities and technical prowess to achieve their malicious objectives.
For more details, visit our website.
Source: Link