Ukraine’s Digital Frontline: PLUGGYAPE Malware Exploits Signal and WhatsApp in Sophisticated Attacks
The Computer Emergency Response Team of Ukraine (CERT-UA) has issued a stark warning regarding a new wave of cyberattacks targeting the nation’s defense forces. Between October and December 2025, a sophisticated malware dubbed PLUGGYAPE has been deployed, with CERT-UA attributing the activity with medium confidence to the Russian hacking group known as Void Blizzard (also tracked as Laundry Bear or UAC-0190), believed to have been active since April 2024.
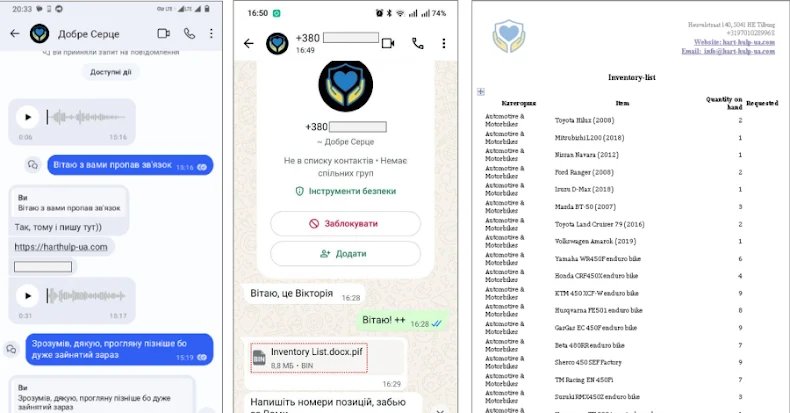
The Deceptive Lure: Social Engineering via Messaging Apps
The attack methodology highlights a disturbing trend: the weaponization of widely used instant messaging platforms. Threat actors are leveraging Signal and WhatsApp, masquerading as legitimate charity organizations to ensnare their targets. Victims are enticed to click on seemingly innocuous links, such as “harthulp-ua[.]com” or “solidarity-help[.]org”, which impersonate aid foundations. These links lead to the download of password-protected archives containing an executable crafted with PyInstaller, ultimately paving the way for the deployment of PLUGGYAPE.
PLUGGYAPE’s Evolving Arsenal
CERT-UA reports that successive iterations of the Python-based PLUGGYAPE backdoor have incorporated advanced obfuscation and anti-analysis checks, specifically designed to thwart execution in virtual environments. This demonstrates a clear effort by the attackers to enhance the malware’s stealth and resilience against detection.
- Dynamic Communication: PLUGGYAPE establishes communication with remote servers via WebSocket or Message Queuing Telemetry Transport (MQTT), the latter protocol having been integrated in December 2025. This allows operators to execute arbitrary code on compromised systems.
- Evasive Command-and-Control (C2): A key operational security measure employed by the attackers involves retrieving C2 addresses from external paste services like rentry[.]co and pastebin[.]com. These addresses are stored in base64-encoded form, rather than being hard-coded directly into the malware. This strategy grants the attackers the flexibility to update C2 servers in real-time, ensuring resilience even if their primary infrastructure is detected and taken down.
The Human Element: A Growing Vulnerability
CERT-UA emphasizes the increasing sophistication of social engineering tactics. “Initial interaction with the target of a cyber attack is increasingly carried out using legitimate accounts and phone numbers of Ukrainian mobile operators, with the use of the Ukrainian language, audio and video communication, and the attacker may demonstrate detailed and relevant knowledge about the individual, organization, and its operations,” the agency stated. This personalized approach, combined with the pervasive use of messengers on mobile and desktop devices, makes these platforms “de facto the most common channel for delivering software tools for cyber threats.”
Broader Cyber Threats to Ukraine’s Infrastructure
The PLUGGYAPE campaign is not an isolated incident. In recent months, CERT-UA has also uncovered other significant threat clusters:
- UAC-0239’s FILEMESS and OrcaC2: This group has been observed sending phishing emails from UKR[.]net and Gmail addresses. These emails contain links to a VHD file or directly attach it, leading to the deployment of FILEMESS, a Go-based stealer that exfiltrates specific file types to Telegram. Additionally, the open-source C2 framework OrcaC2 is dropped, enabling system manipulation, file transfer, keylogging, and remote command execution. These attacks have primarily targeted Ukrainian defense forces and local governments.
- UAC-0241’s LaZagne and GAMYBEAR: Educational institutions and state authorities have been hit by spear-phishing campaigns orchestrated by UAC-0241. These attacks utilize ZIP archives containing malicious Windows shortcut (LNK) files. Opening these files triggers an HTML Application (HTA) via “mshta.exe”, which then executes JavaScript to download and run a PowerShell script. This script delivers LaZagne, an open-source tool for recovering stored passwords, and GAMYBEAR, a Go-based backdoor capable of receiving and executing commands, with results transmitted back in Base64-encoded form over HTTP.
These ongoing threats underscore the relentless and evolving nature of cyber warfare targeting Ukraine, highlighting the critical need for robust cybersecurity defenses and heightened vigilance among its citizens and institutions.
For more details, visit our website.
Source: Link