A sophisticated and patient cyber espionage campaign, attributed to a suspected China-based threat actor, has been systematically targeting military organizations across Southeast Asia since at least 2020. Tracked by Palo Alto Networks Unit 42 under the moniker CL-STA-1087, this state-backed operation demonstrates a clear focus on highly specific intelligence collection rather than indiscriminate data theft, posing a significant threat to regional security.
The Strategic Precision of CL-STA-1087
Unit 42 researchers Lior Rochberger and Yoav Zemah highlight the attackers’ “strategic operational patience” and their meticulous approach to intelligence gathering. Unlike typical cybercriminals seeking financial gain, CL-STA-1087 actively sought and exfiltrated highly sensitive files pertaining to military capabilities, organizational structures, and collaborative efforts with Western armed forces. This level of precision underscores a state-sponsored agenda aimed at acquiring strategic insights.
The campaign bears the hallmarks of an Advanced Persistent Threat (APT) operation, characterized by its carefully engineered delivery methods, robust defense evasion tactics, stable operational infrastructure, and custom payloads designed for prolonged, unauthorized access to compromised systems.
Arsenal of Deception: AppleChris, MemFun, and Getpass
At the core of CL-STA-1087’s toolkit are custom-developed backdoors and credential harvesters, each playing a crucial role in maintaining stealth and achieving objectives.
AppleChris: The Persistent Backdoor
The primary backdoor, AppleChris, is deployed in various versions across target endpoints, ensuring persistence and evading signature-based detection through lateral movement. Its initial access vector remains elusive, but once established, AppleChris communicates with command-and-control (C2) servers to execute a range of commands, including drive enumeration, directory listing, file manipulation (upload, download, deletion), process enumeration, remote shell execution, and silent process creation.
Intriguingly, AppleChris variants utilize shared Pastebin accounts as “dead drop resolvers” to fetch C2 addresses, often Base64-decoded. One version even leverages Dropbox as a primary C2 information source, with Pastebin serving as a fallback. These Pastebin entries date back to September 2020, indicating the campaign’s long-standing nature.
To further bypass automated security systems, some AppleChris variants incorporate sandbox evasion tactics, employing delayed execution timers (30 seconds for EXEs, 120 seconds for DLLs) to outlast typical sandbox monitoring windows.
MemFun: The Modular and Stealthy Threat
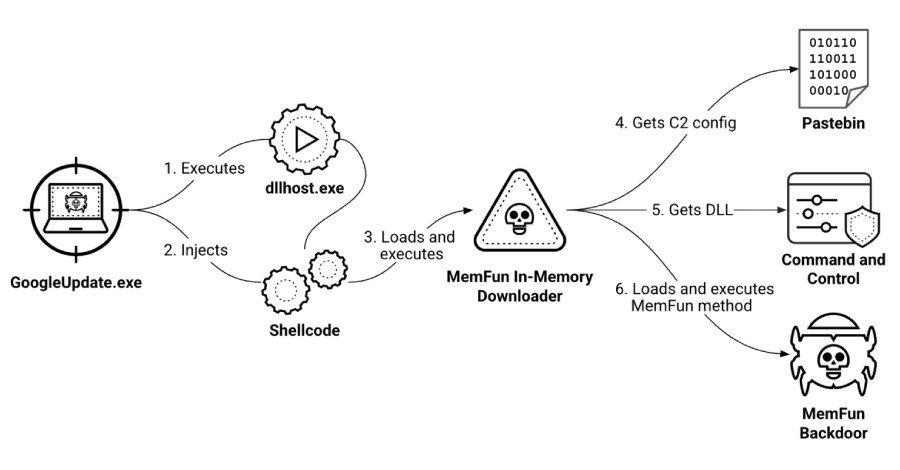
MemFun represents an evolution in the threat actor’s capabilities, functioning as a modular malware platform. Its execution involves a multi-stage chain: an initial loader injects shellcode, which then launches an in-memory downloader. This downloader retrieves C2 configuration from Pastebin, communicates with the C2, and obtains a DLL that triggers the backdoor’s execution. This dynamic delivery mechanism allows threat actors to easily swap payloads without altering the core malware.
MemFun employs advanced anti-forensic techniques, such as altering its file creation timestamp to match legitimate Windows system directories. It also utilizes process hollowing, injecting its main payload into the memory of a suspended “dllhost.exe” process. This allows MemFun to operate under the guise of a legitimate Windows process, minimizing its footprint on disk and evading detection.
Getpass: The Credential Harvester
Complementing the backdoors is Getpass, a customized version of the notorious Mimikatz tool. Getpass is designed to escalate privileges and extract sensitive authentication data, including plaintext passwords, NTLM hashes, and other credentials, directly from the “lsass.exe” process memory. This capability provides the attackers with invaluable access to network resources and further lateral movement opportunities.
Operational Security and Longevity
The CL-STA-1087 cluster exhibits remarkable operational patience and a keen understanding of security protocols. Unit 42 researchers observed attackers maintaining dormant access for months, focusing on precise intelligence collection and implementing robust operational security measures to ensure the campaign’s longevity. Their interest extended to official meeting records, joint military activities, detailed operational capability assessments, and critical C4I (Command, Control, Communications, Computers, and Intelligence) systems.
This sustained, targeted campaign against Southeast Asian military entities underscores the persistent and evolving nature of state-sponsored cyber espionage. It serves as a critical reminder for defense organizations worldwide to bolster their cybersecurity defenses against such sophisticated and patient adversaries.
For more details, visit our website.
Source: Link







Leave a comment