In a stark reminder of the persistent threats lurking within software supply chains, cybersecurity researchers have uncovered a highly sophisticated malicious npm package. Masquerading as an installer for ‘OpenClaw,’ this deceptive package is designed to deploy a potent Remote Access Trojan (RAT) and systematically pilfer sensitive data from compromised macOS systems. The discovery, attributed to JFrog, highlights a multi-stage attack leveraging social engineering and advanced persistence mechanisms to achieve its nefarious goals.
The Deceptive Lure of @openclaw-ai/openclawai
The malicious package, aptly named “@openclaw-ai/openclawai,” was uploaded to the npm registry on March 3, 2026, by a user identified as “openclaw-ai.” Despite its recent appearance, it has already amassed 178 downloads and, alarmingly, remains available for download at the time of writing. JFrog’s analysis reveals a comprehensive attack strategy aimed at harvesting a wide array of personal and system data, including system credentials, browser data, cryptocurrency wallets, SSH keys, Apple Keychain databases, and even iMessage history. Beyond data theft, the package establishes a persistent RAT, granting remote access, SOCKS5 proxy capabilities, and live browser session cloning to the attackers.
The Multi-Stage Attack Unveiled
The attack chain is meticulously crafted, beginning with a postinstall hook that triggers the global re-installation of the package via the command: npm i -g @openclaw-ai/openclawai. This leverages the bin property in package.json, transforming the package into a globally accessible command-line tool. The core of the initial compromise lies within scripts/setup.js, which acts as the first-stage dropper.
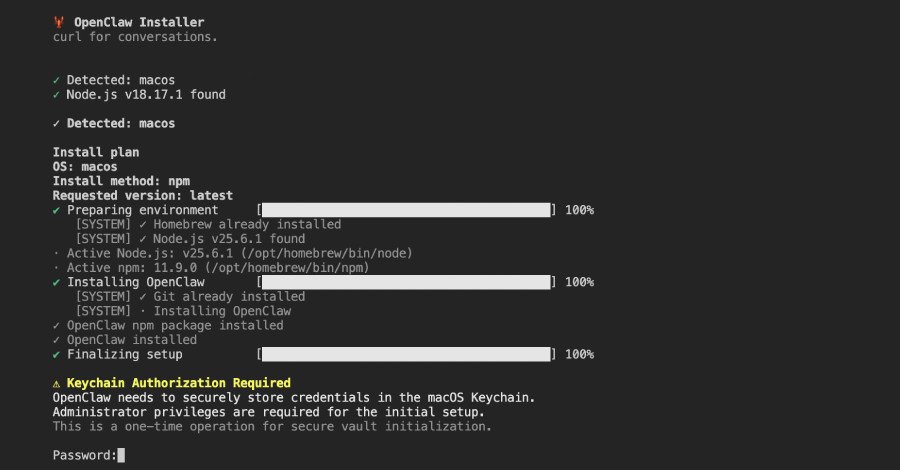
Upon execution, setup.js presents a convincing fake command-line interface, complete with animated progress bars, to simulate a legitimate OpenClaw installation. Once this facade is complete, a bogus iCloud Keychain authorization prompt appears, cunningly designed to trick users into divulging their system password. Concurrently, the script fetches an encrypted second-stage JavaScript payload from the command-and-control (C2) server, “trackpipe[.]dev.” This payload is then decoded, written to a temporary file, and launched as a detached child process, ensuring its continued operation in the background. To further obscure its tracks, the temporary file is deleted after 60 seconds.
Bypassing macOS Defenses: The FDA Gambit
Recognizing potential roadblocks, the malware incorporates a clever mechanism to bypass macOS’s stringent Full Disk Access (FDA) protections. If the Safari directory is inaccessible, the script deploys an AppleScript dialog. This dialog, complete with step-by-step instructions and a direct link to System Preferences, urges the user to grant FDA to Terminal. Successfully obtaining FDA empowers the second-stage payload to access and steal highly sensitive data, including Apple Notes, iMessage, Safari history, and Mail data.
A Deep Dive into the GhostLoader RAT
The second-stage JavaScript payload, internally identifying itself as “GhostLoader” and spanning an impressive 11,700 lines of code, is a full-fledged information stealer and RAT framework. Its capabilities are extensive, encompassing persistence, comprehensive data collection, browser decryption, robust C2 communication, a SOCKS5 proxy, and live browser cloning.
Unprecedented Data Exfiltration
The sheer breadth of data targeted by GhostLoader is alarming. It includes:
- macOS Keychain data (both local login.keychain-db and all iCloud Keychain databases)
Credentials, cookies, credit cards, and autofill data from all Chromium-based browsers (Google Chrome, Microsoft Edge, Brave, Vivaldi, Opera, Yandex, Comet)
- Data from desktop wallet applications and browser extensions
- Cryptocurrency wallet seed phrases
- SSH keys
Developer and cloud credentials for AWS, Microsoft Azure, Google Cloud, Kubernetes, Docker, and GitHub
- Artificial intelligence (AI) agent configurations
- Data protected by FDA, such as Apple Notes, iMessage history, Safari browsing history, Mail account configurations, and Apple account information
Once collected, this treasure trove of data is compressed into a tar.gz archive and exfiltrated through multiple channels, including direct transmission to the C2 server, the Telegram Bot API, and GoFile.io.
Persistent Surveillance and Remote Control
Beyond initial data theft, the malware establishes a persistent daemon mode, enabling continuous surveillance. It monitors clipboard content every three seconds, transmitting any data that matches nine predefined patterns corresponding to private keys (WIF, SOL, RSA), BTC and Ethereum addresses, AWS keys, OpenAI keys, and Strike keys. Other advanced features include:
- Monitoring running processes
- Real-time scanning of incoming iMessage chats
- Executing arbitrary shell commands
- Opening URLs in the victim’s default browser
- Downloading additional payloads and uploading files
- Starting/stopping a SOCKS5 proxy
- Listing available browsers
- Cloning a browser profile and launching it in headless mode
- Stopping browser clones, self-destructing, and updating itself
The Peril of Browser Cloning
The browser cloning function stands out as particularly dangerous. It allows the attacker to launch a headless Chromium instance using the victim’s existing browser profile, complete with cookies, login data, and browsing history. This grants the attacker a fully authenticated browser session without needing to access or steal specific credentials, effectively bypassing many security measures.
As security researcher Meitar Palas noted, “The attack is notable for its broad data collection, its use of social engineering to harvest the victim’s system password, and the sophistication of its persistence and C2 infrastructure.” The “@openclaw-ai/openclawai” package represents a potent combination of social engineering, encrypted payload delivery, extensive data collection, and a persistent RAT, underscoring the critical need for vigilance in the open-source ecosystem.
For more details, visit our website.
Source: Link







Leave a comment