In a startling development that underscores the precarious nature of digital security, a highly sophisticated iPhone-hacking toolkit, dubbed “Coruna,” appears to have embarked on a disturbing journey from suspected state-sponsored actors to opportunistic cybercriminals. This powerful exploit, capable of indiscriminately hijacking iOS devices through mere website visits, raises profound questions about the proliferation of advanced cyber weaponry and its potential origins within the US government.
Coruna: A Deep Dive into a Potent Exploit
Security researchers at Google recently unveiled details about Coruna, a formidable toolkit comprising five distinct hacking techniques. These methods are designed to bypass all of an iPhone’s native defenses, silently installing malware when a user simply navigates to a compromised website. In total, Coruna leverages an astonishing 23 unique vulnerabilities within iOS, a complexity that strongly suggests the involvement of a well-resourced, likely state-sponsored, development team.
Google’s investigation traces elements of Coruna back to February of last year, where it was first observed in use by a “customer of a surveillance company.” Just five months later, a more complete iteration of Coruna resurfaced, deployed in what appeared to be an espionage campaign by a suspected Russian spy group. This group cleverly embedded the hacking code within a common visitor-counting component on Ukrainian websites, targeting unsuspecting users.
The saga didn’t end there. Google subsequently detected Coruna in a purely profit-driven cybercriminal operation. This time, the exploit was found infecting Chinese-language cryptocurrency and gambling sites, designed to steal digital assets from victims.
The Uncomfortable Question of Origin: A US Connection?
While Google’s report refrains from identifying the original “surveillance company customer,” mobile security firm iVerify offers a provocative theory: Coruna may have originated as a hacking kit built for, or purchased by, the US government. Both Google and iVerify highlight that Coruna shares components with “Triangulation,” a hacking operation discovered in 2023 targeting Russian cybersecurity giant Kaspersky, which the Russian government controversially attributed to the NSA.
Further bolstering this theory, iVerify’s cofounder, Rocky Cole, notes that Coruna’s code appears to have been initially penned by English-speaking developers. “It’s highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government,” Cole revealed to WIRED. He added, “This is the first example we’ve seen of very likely US government tools—based on what the code is telling us—spinning out of control and being used by both our adversaries and cybercriminal groups.”
An “EternalBlue Moment” for Mobile Security
Regardless of its precise genesis, Coruna’s journey through multiple, disparate hands is a grave concern. Google warns that this exceptionally valuable and rare hacking toolkit is now “in the wild,” ripe for adoption or adaptation by any threat actor seeking to compromise iPhone users. The report suggests an “active market for ‘second hand’ zero-day exploits,” where sophisticated techniques can be acquired, reused, and modified.
Rocky Cole draws a stark parallel to the infamous “EternalBlue” incident. EternalBlue, a Windows-hacking tool stolen from the National Security Agency and leaked in 2017, fueled catastrophic cyberattacks worldwide, including North Korea’s WannaCry worm and Russia’s NotPetya attack. If Coruna indeed began as a US government tool, its leakage represents a similar “EternalBlue moment” for mobile malware, raising critical questions about the security of highly potent cyber weapons once they leave official control.
Protection and Limitations
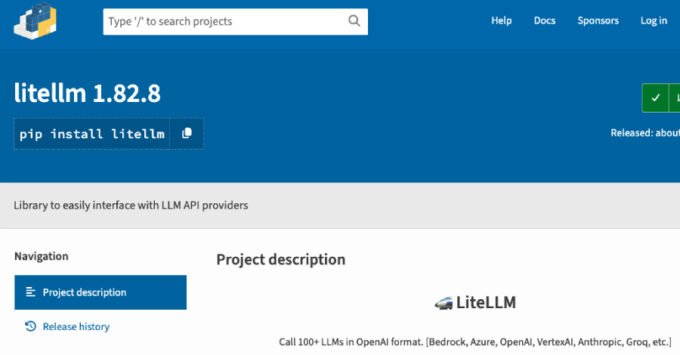
Fortunately, Apple has addressed the vulnerabilities exploited by Coruna in recent iOS updates. The toolkit’s exploitation techniques are confirmed to be effective only against iOS versions 13 through 17.2.1. It specifically targets flaws within Apple’s Webkit framework, meaning Safari users on older iOS versions are at risk. There are no confirmed techniques within Coruna for targeting Chrome users. Additionally, Google notes that Coruna intelligently checks for Apple’s stringent Lockdown Mode and will not attempt to exploit devices with this security setting enabled.
Despite these limitations, the saga of Coruna serves as a potent reminder of the constant arms race in cybersecurity and the perilous implications when advanced state-level tools fall into the wrong hands.
For more details, visit our website.
Source: Link




Leave a comment