A significant security flaw, dubbed “ClawJacked,” has been identified and patched in the OpenClaw AI agent ecosystem. This high-severity vulnerability could have allowed malicious websites to silently connect to and seize control of locally running OpenClaw AI agents, posing a substantial risk to developers and enterprises alike.
According to a report by Oasis Security, the flaw was not hidden within plugins or extensions but resided “in the core system itself – just the bare OpenClaw gateway, running exactly as documented.” This highlights a fundamental design oversight that granted undue trust to local connections.
Understanding the ClawJacked Attack
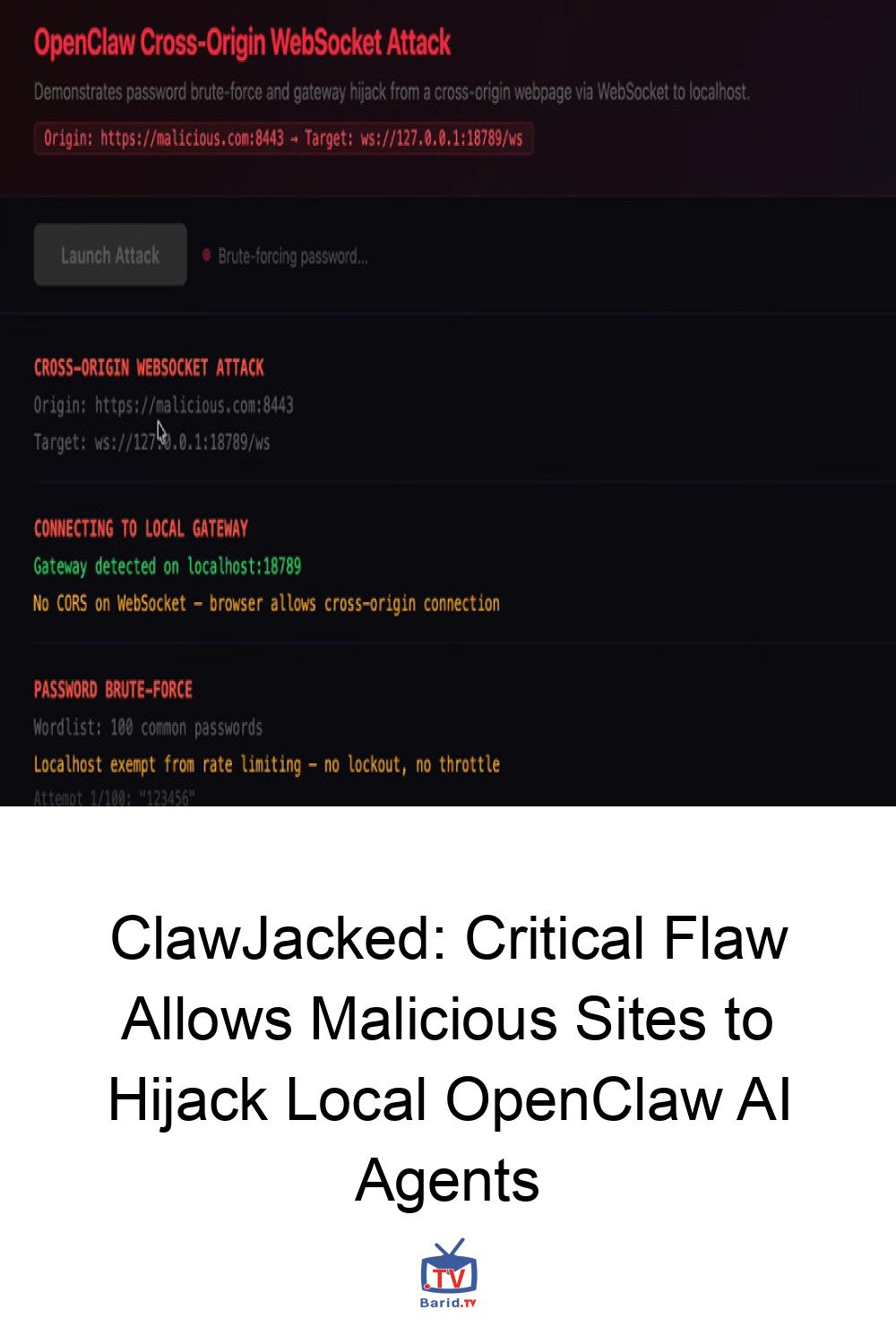
The ClawJacked vulnerability exploits a critical weakness in how OpenClaw’s local WebSocket server, typically bound to localhost and password-protected, handles connections. The attack scenario unfolds as follows:
The Silent Intrusion
- A developer, with OpenClaw running on their laptop, is lured to an attacker-controlled website, perhaps through social engineering.
- Malicious JavaScript embedded on this webpage initiates a WebSocket connection to the OpenClaw gateway port on the developer’s localhost. Crucially, web browsers do not block these cross-origin connections to localhost, making the process invisible to the user.
- The script then brute-forces the gateway password, leveraging a critical absence of rate-limiting, which would normally prevent such rapid, repeated authentication attempts.
- Upon successful authentication with administrative privileges, the script stealthily registers itself as a trusted device. The OpenClaw gateway, operating under a “misplaced trust” for local connections, auto-approves this registration without any user prompt – a step that would typically require explicit confirmation for remote devices.
Once registered, the attacker gains complete control over the AI agent. This allows them to interact with it, extract sensitive configuration data, enumerate connected nodes, and access application logs, effectively turning the developer’s local AI agent into a tool for further malicious activity.
A Broader Look at OpenClaw Security
The ClawJacked disclosure comes amidst increasing scrutiny of the entire OpenClaw ecosystem. AI agents, by their very nature, often possess extensive access to disparate systems and the authority to execute tasks across various enterprise tools. This makes them high-value targets, as their compromise can lead to a significantly larger “blast radius.”
The Threat of Prompt Injections and Log Poisoning
Reports from cybersecurity firms like Bitsight and NeuralTrust have previously warned that OpenClaw instances exposed to the internet present an expanded attack surface. Each integrated service broadens this surface, making agents susceptible to prompt injection attacks. Malicious instructions can be embedded within content (e.g., an email or Slack message) processed by the agent, compelling it to perform unintended actions.
In a related development, OpenClaw also recently patched a log poisoning vulnerability. This flaw allowed attackers to write malicious content to log files via WebSocket requests to publicly accessible instances. Since AI agents often read their own logs for troubleshooting, this loophole could be exploited to embed indirect prompt injections, subtly manipulating the agent’s reasoning, influencing troubleshooting steps, or even leading to data disclosure.
A String of Recent Vulnerabilities
Beyond these specific issues, OpenClaw has been grappling with a series of other vulnerabilities (CVE-2026-25593, CVE-2026-24763, CVE-2026-25157, CVE-2026-25475, CVE-2026-26319, CVE-2026-26322, CVE-2026-26329). These range from moderate to high severity and could facilitate remote code execution, command injection, server-side request forgery (SSRF), authentication bypass, and path traversal. These issues underscore the complex security challenges inherent in rapidly evolving AI frameworks.
Immediate Action and Future Safeguards
OpenClaw demonstrated responsible disclosure by issuing a fix for the ClawJacked vulnerability in less than 24 hours, with version 2026.2.25 released on February 26, 2026. The log poisoning issue was addressed earlier in version 2026.2.13 (February 14, 2026), and other vulnerabilities in versions 2026.1.20, 2026.1.29, 2026.2.1, 2026.2.2, and 2026.2.14.
Users are strongly advised to apply these latest updates immediately. Furthermore, cybersecurity experts recommend:
- Periodically auditing access permissions granted to AI agents.
- Enforcing robust governance controls for non-human (agentic) identities.
- Maintaining vigilance against social engineering tactics.
“As AI agent frameworks become more prevalent in enterprise environments, security analysis must evolve to address both traditional vulnerabilities and AI-specific attack surfaces,” notes Endor Labs. The emergence of malicious “skills” on marketplaces like ClawHub, used to deliver malware such as the Atomic Stealer for macOS, further emphasizes the urgent need for comprehensive security strategies in the AI domain.
For more details, visit our website.
Source: Link