Beyond Isolated Threats: Embracing Continuous Threat Exposure Management (CTEM)
In the dynamic landscape of modern cybersecurity, simply identifying threats and vulnerabilities in isolation is no longer sufficient. Security teams are increasingly recognizing the critical need to understand where these potential weaknesses intersect within their unique environments, creating tangible, exploitable exposures. The crucial questions have shifted: Which exposures truly matter? Can attackers realistically exploit them? And are our existing defenses genuinely effective?
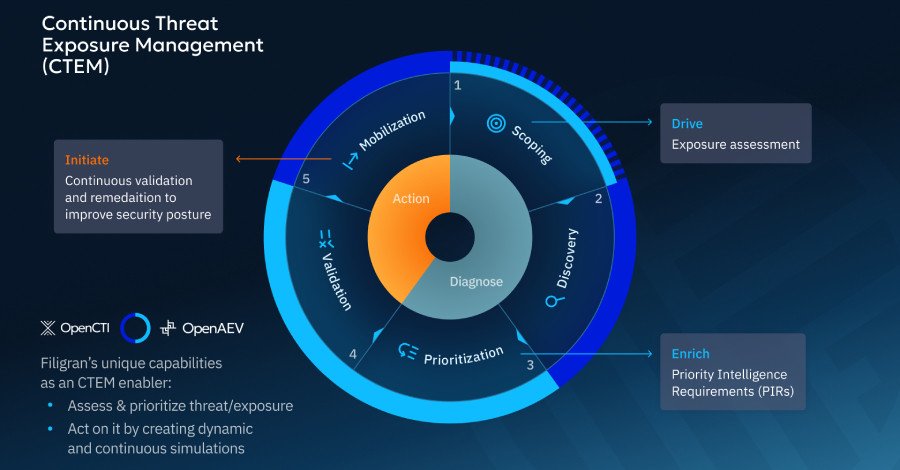
Enter Continuous Threat Exposure Management (CTEM) – a strategic, unified approach designed to guide cybersecurity teams on their journey towards comprehensive exposure management. CTEM moves beyond reactive scanning, offering a proactive framework to systematically identify, prioritize, and mitigate the risks that pose the greatest threat to an organization.
What is CTEM, Really? A Strategic Framework for Modern Security
As defined by Gartner, CTEM is not a product, but an operational model emphasizing a ‘continuous’ cycle. Its core objective is to identify, prioritize, and remediate exploitable exposures across your entire attack surface, leading to a measurable improvement in your overall security posture. This isn’t a one-off assessment; it’s an ongoing, iterative process built upon five fundamental steps:
- Scoping: Begin by clearly defining your most critical assets, processes, and potential adversaries. This initial assessment sets the boundaries for your exposure management program.
- Discovery: Proactively map exposures and potential attack paths across your environment, anticipating how an adversary might move and exploit weaknesses.
- Prioritization: Focus your efforts on exposures that attackers can realistically exploit, rather than every theoretical vulnerability. This step ensures resources are directed where they matter most.
- Validation: Test your assumptions and the effectiveness of your controls through safe, controlled attack simulations. This provides empirical evidence of your security posture.
- Mobilization: Drive targeted remediation and continuous process improvements based on the evidence gathered during validation, ensuring a proactive and adaptive defense.
Unlocking True Value: The Tangible Benefits of a CTEM Approach
CTEM represents a fundamental shift towards risk-based exposure management. It seamlessly integrates numerous sub-processes and tools—from vulnerability assessment and management to attack surface management, testing, and simulation—into a cohesive strategy. By unifying exposure assessment and validation, CTEM empowers security teams to accurately record and report the potential impact on cyber risk reduction.
The cybersecurity industry has long grappled with an abundance of tools, often leading to fragmented views and siloed operations. CTEM directly challenges this paradigm, aiming to unify our understanding of threats, vulnerabilities, and attack surfaces. Its ultimate goal is to enable decisive action against truly exploitable exposures, thereby achieving a quantifiable reduction in overall cyber risk.
The Indispensable Role of Threat Intelligence
Consider this: while over 40,000 vulnerabilities were reported in 2024 alone, less than 10% are ever actively exploited. This stark reality underscores the critical need for effective prioritization. Threat intelligence (TI) is no longer a ‘good-to-have’ but a ‘need-to-have’ capability. It significantly helps organizations zero in on the vulnerabilities that genuinely matter by connecting them to adversary tactics, techniques, and procedures (TTPs) observed in active campaigns.
By leveraging TI, organizations can specify Priority Intelligence Requirements (PIRs), defining the specific context and threat landscape most relevant to their environment. This prioritized intelligence reveals which flaws are being weaponized, against which targets, and under what conditions, allowing teams to focus remediation efforts on what’s truly exploitable, rather than what’s merely theoretically possible. The key question for any threat intelligence team should be: Are we optimizing the value from the threat data we collect today?
From Prioritization to Proof: Validation-Driven Risk Reduction
Prioritized threat intelligence must be followed by rigorous testing and validation. This crucial step assesses how your security controls stand up against the most probable exploits and attack paths, and critically, what impact a successful breach could have on your organization. It’s vital that your security validation program extends beyond technology to encompass processes and people.
Even perfectly tuned EDR, SIEM, or WAF solutions offer limited protection if incident workflows are unclear, playbooks are outdated, or escalation paths fail under pressure. This holistic approach is driving a convergence of breach & attack simulation, tabletop exercises, and automated pen-testing towards what we term Adversarial Exposure Validation (AEV).
Implementing CTEM: A Strategic Journey, Not a Product Purchase
It bears repeating: CTEM is not a product you buy; it’s a strategic approach leveraging outcome-driven metrics for comprehensive exposure management. Its successful implementation requires leadership from the top, breaking down organizational silos, and fostering improved security workflows across all teams.
To embark on your CTEM journey, begin with the ‘Scoping’ stage. Ask critical questions to define your program’s initial focus:
- What are our top business risks that cybersecurity can directly influence?
- Which environments (on-prem, cloud, IT/OT, subsidiaries) and asset types (crown jewels, endpoints, identity systems, data stores) are in scope? Do we have an accurate inventory?
- Which threat actors and attack methods are most relevant to our industry and tech stack?
- How will we incorporate existing threat intelligence and incident data to refine our scope?
- How will we define ‘critical exposure’ (based on exploitability, business impact, data sensitivity, blast radius, etc.)?
- Are we currently able to validate our tools, people, and processes? What is our initial capacity for this?
By answering these questions, organizations can lay a robust foundation for a CTEM program that delivers meaningful, measurable improvements in their cyber resilience.
For more details, visit our website.
Source: Link