A recent disclosure has sent ripples through the AI development community, revealing a trio of critical security vulnerabilities within mcp-server-git, Anthropic’s official Git Model Context Protocol (MCP) server. These flaws, if exploited, could grant attackers unprecedented access, allowing them to read or delete arbitrary files and even execute malicious code under specific conditions.
The severity of these vulnerabilities is amplified by their exploit mechanism: prompt injection
. As Cyata researcher Yarden Porat highlighted in a report shared with The Hacker News, “These flaws can be exploited through prompt injection, meaning an attacker who can influence what an AI assistant reads (a malicious README, a poisoned issue description, a compromised webpage) can weaponize these vulnerabilities without any direct access to the victim’s system.” This means a seemingly innocuous piece of data could become a potent weapon, turning an AI assistant into an unwitting accomplice.
Understanding the Threat: Anthropic’s MCP Git Server
Mcp-server-git is a Python package designed as an MCP server, providing a suite of built-in tools for large language models (LLMs) to programmatically interact with Git repositories – reading, searching, and manipulating them. Its role as a foundational component for AI-driven Git operations makes its security paramount.
The identified security issues, responsibly disclosed in June 2025 and subsequently addressed in versions 2025.9.25 and 2025.12.18, are detailed below:
CVE-2025-68143: Path Traversal in git_init (CVSS v3: 8.8 / v4: 6.5)
This vulnerability stems from the git_init tool’s failure to validate arbitrary file system paths during repository creation. An attacker could exploit this to create a Git repository in an unintended location, potentially overwriting or interfering with critical system files. This flaw was patched in version 2025.9.25.
CVE-2025-68144: Argument Injection in git_diff and git_checkout (CVSS v3: 8.1 / v4: 6.4)
The git_diff and git_checkout functions were found to pass user-controlled arguments directly to Git CLI commands without proper sanitization. This opens the door for argument injection, where an attacker could inject malicious commands into the Git CLI, leading to unauthorized actions. This issue was resolved in version 2025.12.18.
CVE-2025-68145: Path Traversal with –repository Flag (CVSS v3: 7.1 / v4: 6.3)
A third path traversal vulnerability was identified due to a lack of path validation when the --repository flag was used to restrict operations to a specific repository path. This could allow an attacker to bypass intended restrictions and access repositories outside the specified path. This was also fixed in version 2025.12.18.
The Chilling Potential: Remote Code Execution via Prompt Injection
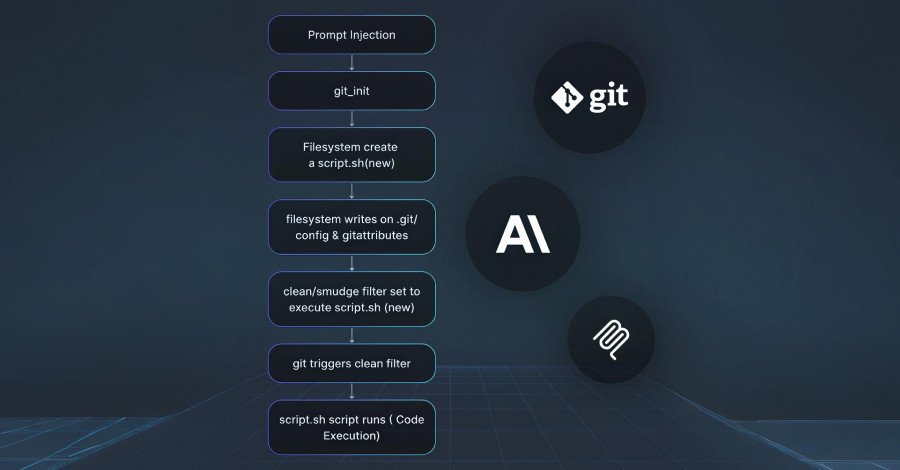
Individually, these vulnerabilities pose significant risks. However, their true danger emerges when chained together. Cyata researchers demonstrated a sophisticated attack scenario where all three could be combined with the Filesystem MCP server to achieve remote code execution (RCE).
The attack chain unfolds as follows:
- Utilize
git_init(CVE-2025-68143) to create a repository in a writable directory. - Leverage the Filesystem MCP server to write a malicious
.git/configfile, embedding a “clean filter.” - Create a
.gitattributesfile to apply this malicious filter to specific files. - Write a shell script containing the desired payload.
- Create a file that, when processed, triggers the malicious filter.
- Call
git_add, which then executes the clean filter, running the attacker’s payload and achieving RCE.
This intricate sequence underscores the critical nature of prompt injection, transforming seemingly harmless AI interactions into a pathway for system compromise.
Anthropic’s Swift Response and Industry Implications
In light of these findings, Anthropic has taken decisive action. The git_init tool has been entirely removed from the package, and additional validation measures have been implemented to thwart path traversal attempts. Users of the Python package are strongly advised to update to the latest versions (2025.9.25 or 2025.12.18, depending on the specific fix) to ensure optimal protection.
Shahar Tal, CEO and co-founder of Agentic AI security company Cyata, emphasized the broader implications: “This is the canonical Git MCP server, the one developers are expected to copy. If security boundaries break down even in the reference implementation, it’s a signal that the entire MCP ecosystem needs deeper scrutiny. These are not edge cases or exotic configurations, they work out of the box.” His statement serves as a stark reminder that as AI systems become more integrated into core infrastructure, the security of their underlying components is paramount, demanding rigorous, proactive scrutiny across the entire ecosystem.
Stay informed on critical cybersecurity developments. Follow us on Google News, Twitter, and LinkedIn for more exclusive content.
For more details, visit our website.
Source: Link